
March 05, 2026
Healthcare
How to Modernize Legacy Healthcare Software While Staying FDA and HIPAA Compliant
Key Takeaways
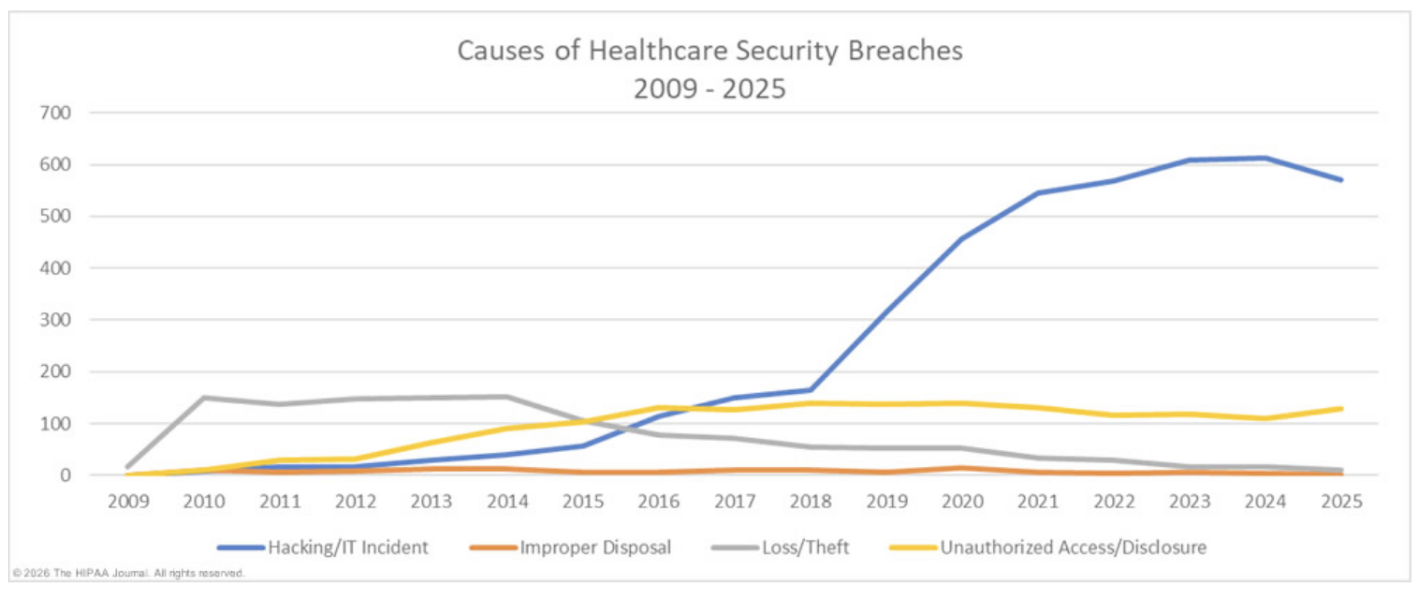 Source: HIPAA Journal
Then there are the integration problems. Most legacy systems in healthcare were not built with FHIR or HL7 standards in mind. That means connecting them to newer platforms, whether it is a telehealth system, a patient portal, or an analytics tool, requires expensive custom middleware and workarounds.
Source: HIPAA Journal
Then there are the integration problems. Most legacy systems in healthcare were not built with FHIR or HL7 standards in mind. That means connecting them to newer platforms, whether it is a telehealth system, a patient portal, or an analytics tool, requires expensive custom middleware and workarounds.
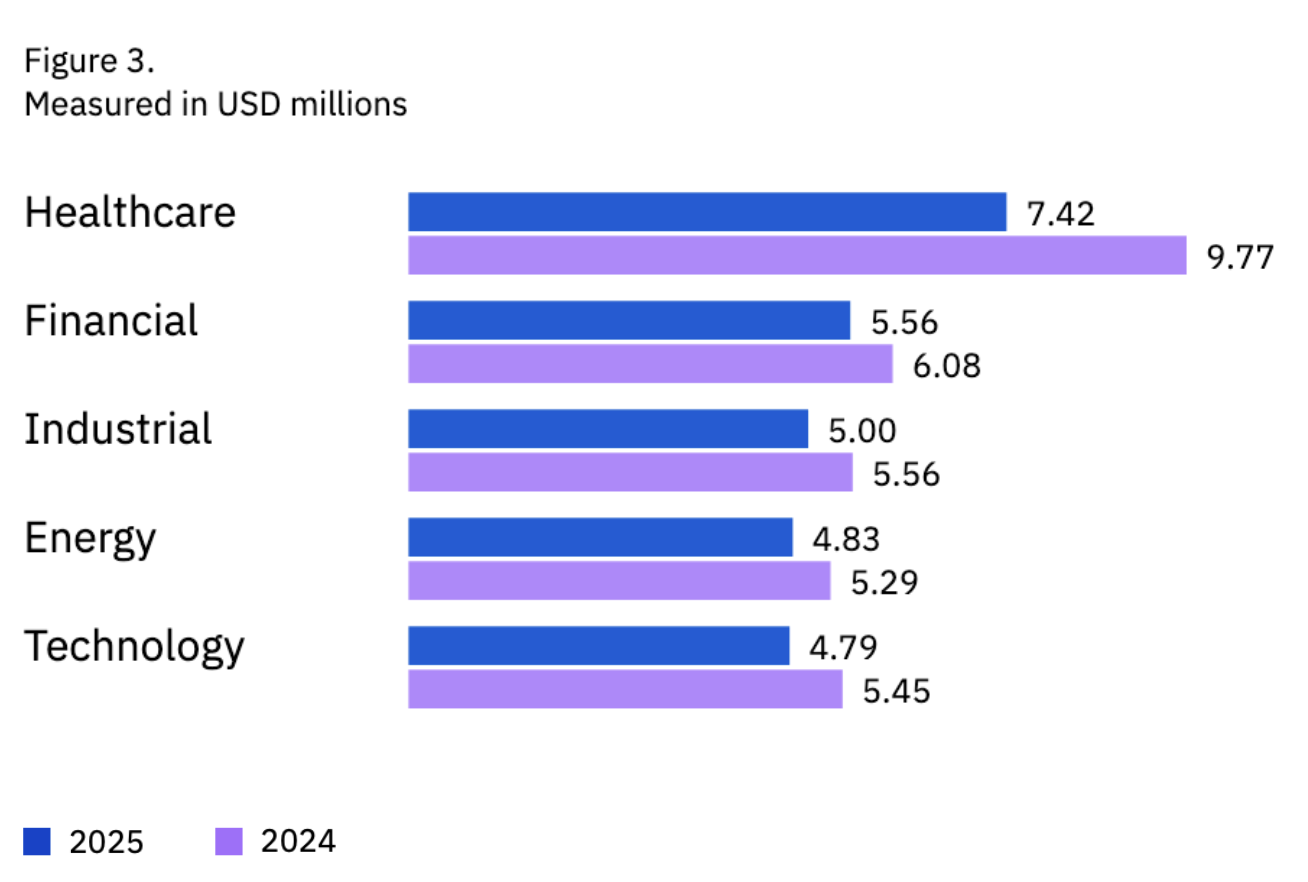 Average breach cost by sector. Source: IBM
Average breach cost by sector. Source: IBM
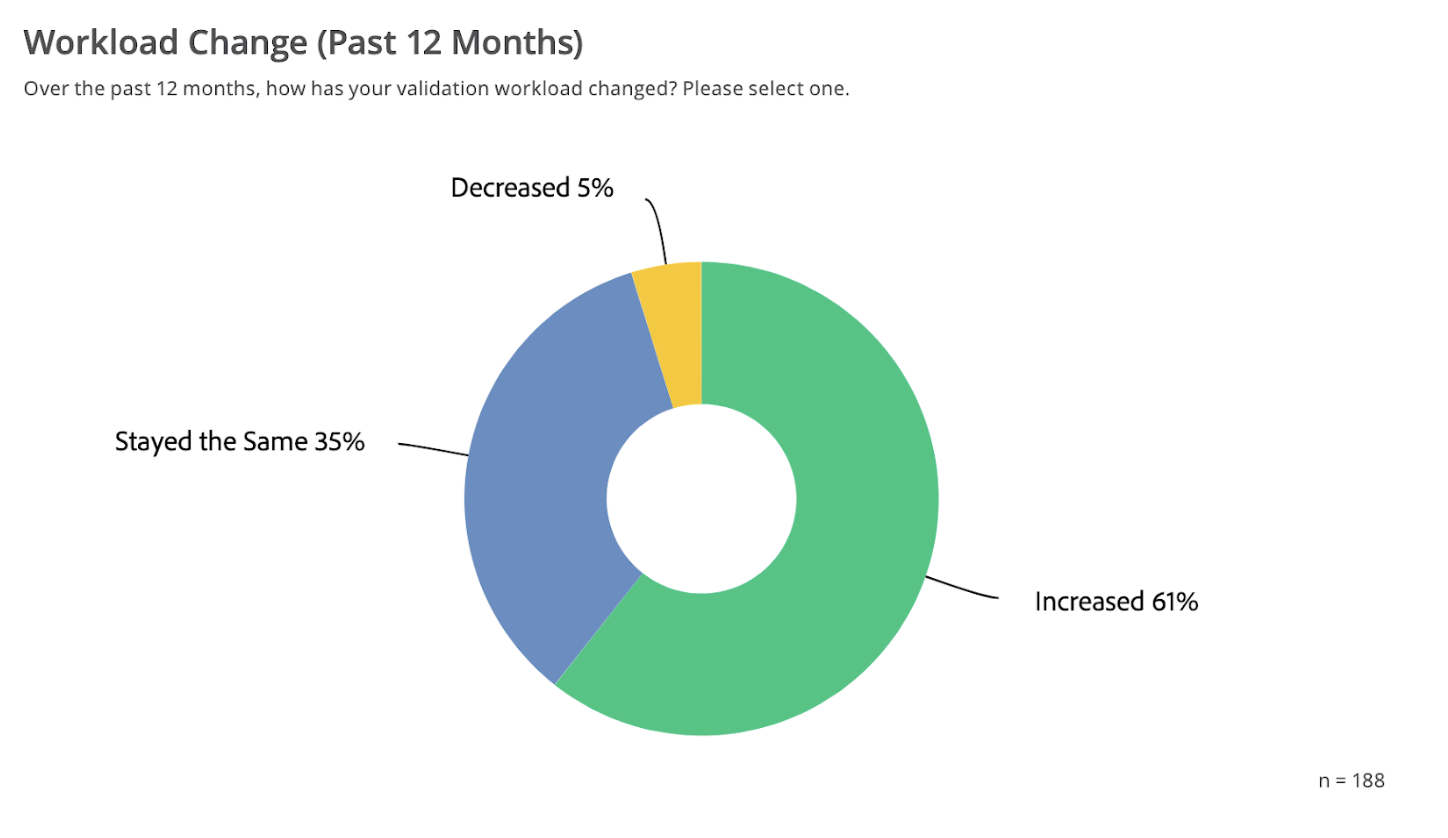 Source: State of Validation Report
Source: State of Validation Report
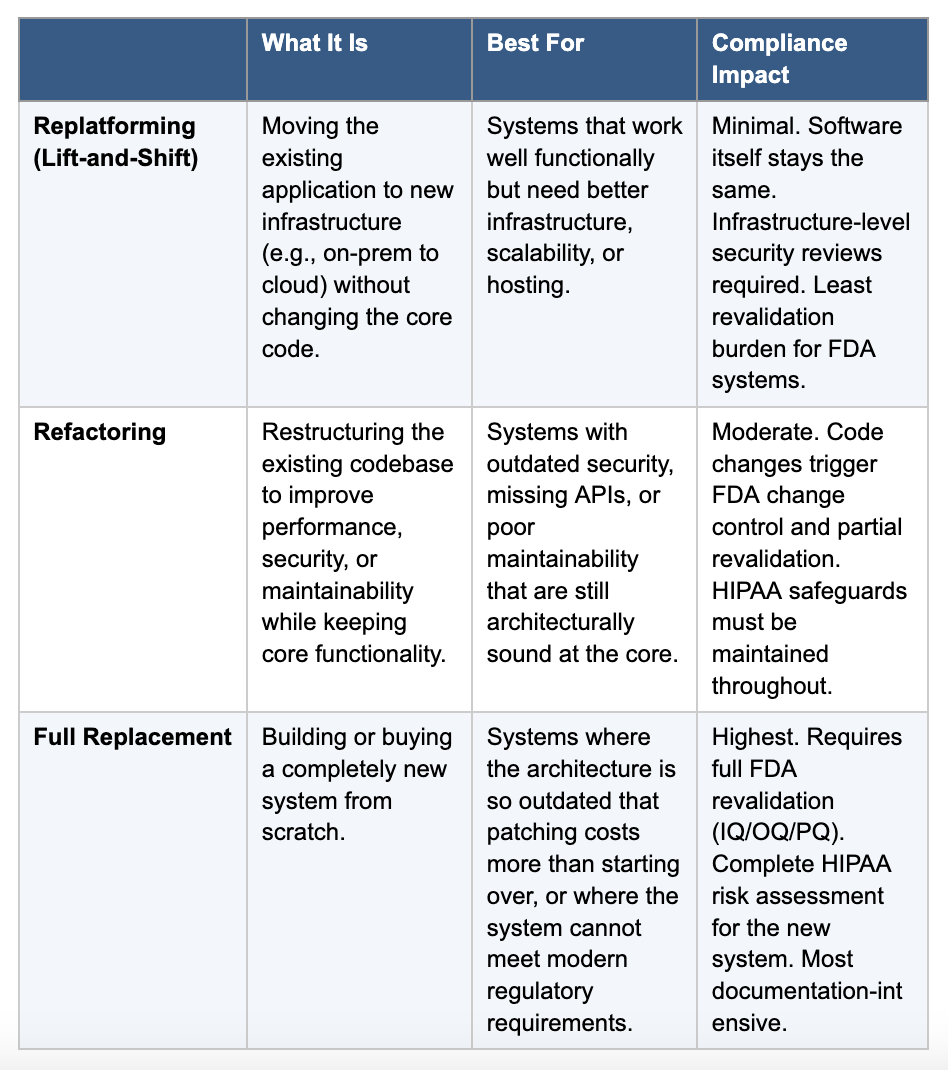 Note: For FDA-regulated software, refactoring and replacement both trigger significant revalidation requirements. Factor that into your timeline and budget from the start.
Note: For FDA-regulated software, refactoring and replacement both trigger significant revalidation requirements. Factor that into your timeline and budget from the start.
- Over 60% of U.S. hospitals still run critical applications on legacy software.
- Most healthcare organizations spend up to 75% of their IT budgets just maintaining outdated systems.
- Any change to FDA-regulated or HIPAA-covered software triggers compliance requirements that must be planned for upfront.
- Phased modernization reduces risk to clinical operations and keeps compliance intact throughout the transition.
- Modular, API-first architectures prevent today’s new systems from becoming tomorrow’s legacy problems.
Where to Begin: Your 5-Step Modernization Roadmap
If you are a healthcare leader looking at an aging system and wondering where to start, here is a high-level roadmap. Each step is covered in more detail throughout the guide.- Assess your current systems. Catalog every legacy application, document its compliance status (FDA-regulated? HIPAA-covered?), and identify the highest-risk components—the ones with the most security exposure, the heaviest maintenance costs, or the most integration bottlenecks.
- Understand your compliance obligations. Map out which regulations apply to each system. Know upfront what will trigger FDA revalidation, what HIPAA safeguards are required during data migration, and what documentation you will need for audits.
- Choose the right modernization approach. Decide whether to replatform, refactor, or replace each system based on its architecture, compliance footprint, and business value. Use the comparison table below to guide your decision.
- Plan a phased implementation. Break the project into stages. Migrate one module at a time, validate compliance at each step, and run parallel environments so you can catch problems before they affect clinical operations.
- Build for the future. Design with modular, API-first architectures and continuous compliance monitoring so you do not end up in the same situation five years from now.
The State of Legacy Healthcare Software Today
Many of the platforms still running in hospitals today were built on architectures like AS/400, early .NET frameworks, or COBOL-based mainframes. They were solid for their time. But they were never designed to handle modern interoperability standards, real-time data exchange, or the cybersecurity threats that exist today.Technical Risks That Compound Over Time
Legacy systems carry risk that grows the longer you wait. Outdated IT systems stop receiving vendor support and security patches, which turns them into open doors for attackers. A SOTI report found that 83% of healthcare organizations experienced a healthcare system breach in the past two years, and outdated software was among the leading causes. On top of that, data tracked by the HIPAA Journal showed that over 275 million healthcare records were exposed or stolen in 2024 alone—a 60% increase from the year before.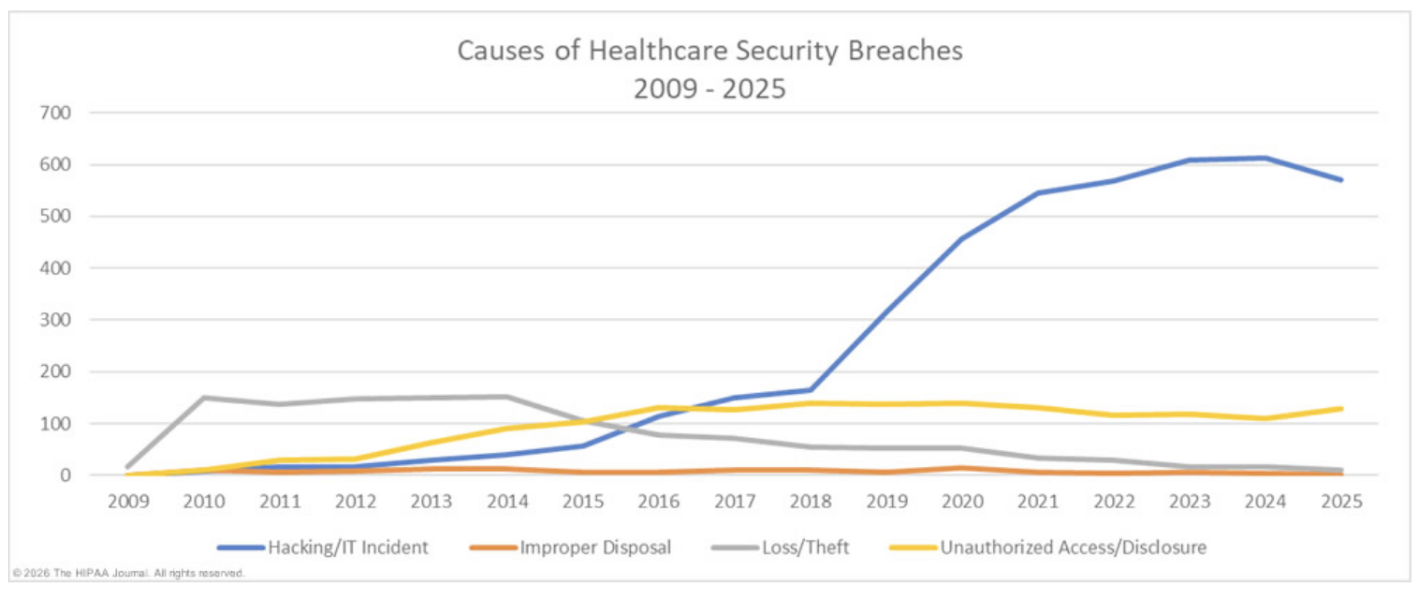 Source: HIPAA Journal
Then there are the integration problems. Most legacy systems in healthcare were not built with FHIR or HL7 standards in mind. That means connecting them to newer platforms, whether it is a telehealth system, a patient portal, or an analytics tool, requires expensive custom middleware and workarounds.
Source: HIPAA Journal
Then there are the integration problems. Most legacy systems in healthcare were not built with FHIR or HL7 standards in mind. That means connecting them to newer platforms, whether it is a telehealth system, a patient portal, or an analytics tool, requires expensive custom middleware and workarounds.
The Business Cost of Standing Still
The healthcare business case for modernization is just as compelling as the technical one. When 75% of your IT budget is going toward keeping old systems alive, you’re essentially paying a tax on outdated technology—driving up operational costs without making anything run better. That money could be put toward better patient engagement tools, modern web-based platforms, or clinical decision support systems. And the cost of a breach makes the math even worse. According to IBM’s Cost of a Data Breach Report, healthcare breaches now cost an average of $10.93 million per incident, which is more than any other industry. A lot of that exposure comes from the exact kind of outdated infrastructure we are talking about: unpatched software, weak access controls, and audit logging that does not meet current standards.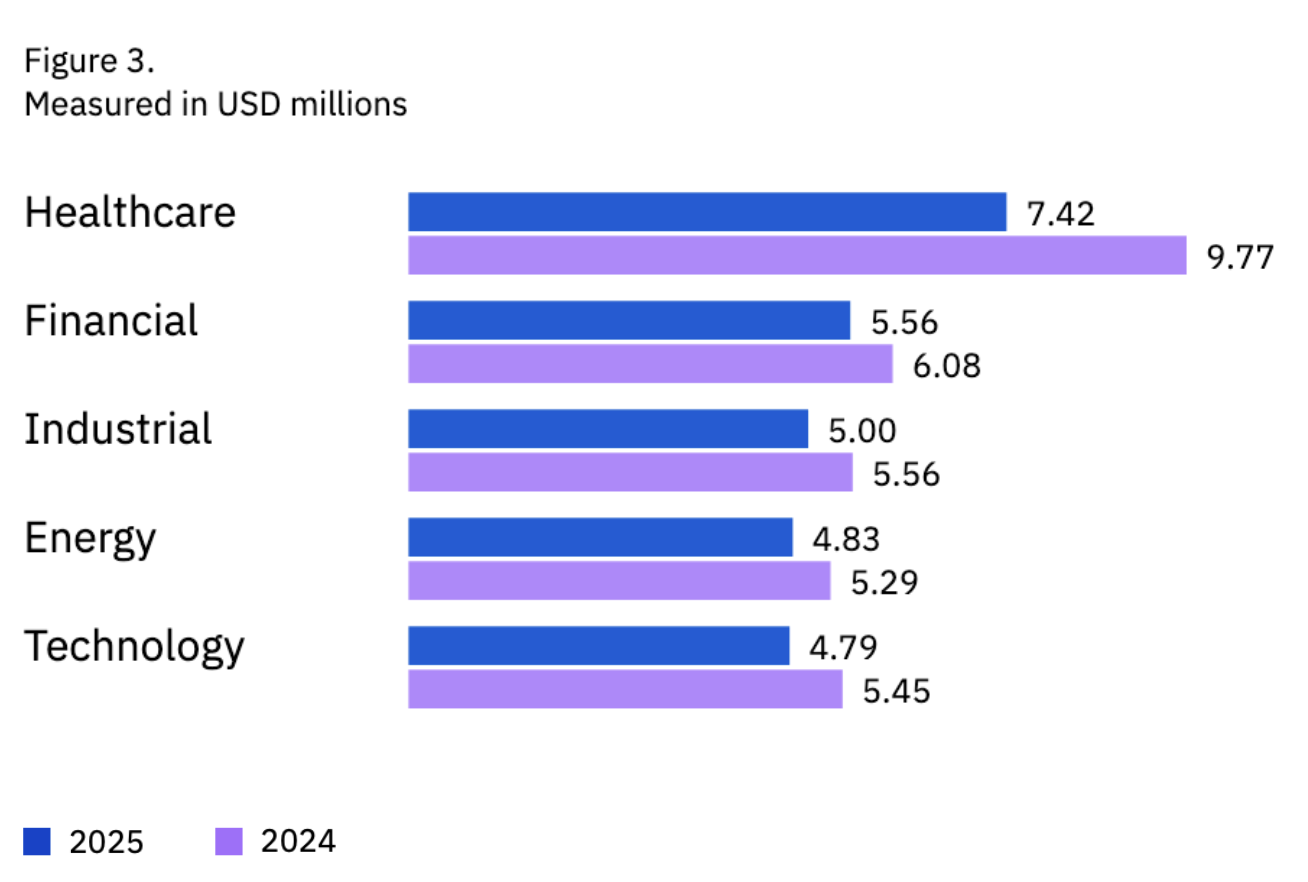 Average breach cost by sector. Source: IBM
Average breach cost by sector. Source: IBM
Understanding FDA and HIPAA Compliance Requirements
Before you start ripping out old systems and replacing them with new ones, you need a clear picture of what the regulators actually require. FDA and HIPAA compliance shape every decision you make during a modernization project, from how you migrate data to how you test and validate new systems.FDA Software Validation and 21 CFR Part 11
If your software qualifies as a medical device, or as Software as a Medical Device (SaMD), it falls under FDA oversight. The big regulation to know here is 21 CFR Part 11, which sets the rules for electronic records and electronic signatures. In practical terms, this means your system needs to have:- Validated audit trails that log every action
- Secure access controls with role-based permissions
- Documentation that proves the software does what it claims to do
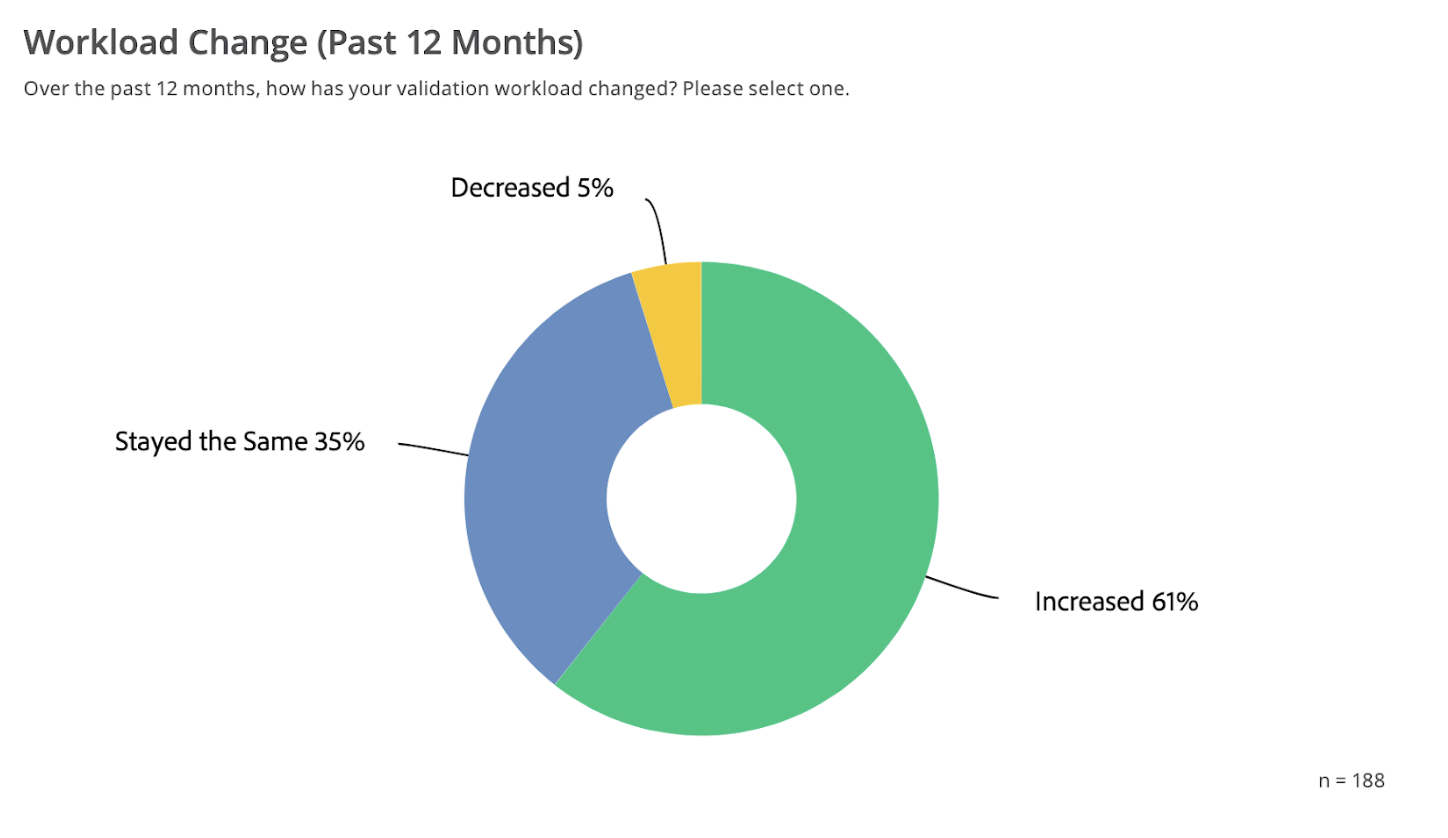 Source: State of Validation Report
Source: State of Validation Report
HIPAA During System Transitions
HIPAA’s Security Rule lays out the technical safeguards your systems need: access controls, audit controls, data integrity mechanisms, and transmission security. The Privacy Rule governs how Protected Health Information (PHI) can be used and disclosed. Both of these matter a lot during a system transition where the goal is to ensure regulatory compliance while migrating sensitive data. Data migration is where most HIPAA risks show up. During any system transition, you need to ensure:- Encryption in transit and at rest for all PHI
- Detailed access logging throughout the migration
- Rollback procedures in case something goes wrong
- Updated Business Associate Agreements (BAAs) if third-party vendors are involved
- A Breach Notification plan—if PHI gets exposed during the transition, you are on the hook to report it within 60 days
Healthcare Compliance Audits During Modernization
Modernization projects tend to draw auditor attention. A healthcare compliance audit during a system transition will look at whether you maintained continuous compliance throughout the process, not just before and after. This means you need documentation showing:- PHI was protected at every stage
- Access controls were never weakened
- Data governance policies remained intact
- Validation protocols held up even while systems were being swapped out
Choosing Your Modernization Approach
Not every legacy system needs the same treatment. Some can be incrementally updated. Others need to be rebuilt from the ground up. The right approach depends on a few factors: how deeply the system is embedded in your operations, what your compliance obligations are, and how much risk your organization can absorb at once.Replatform, Refactor, or Replace
There are three main paths, and each has trade-offs. The table below breaks them down: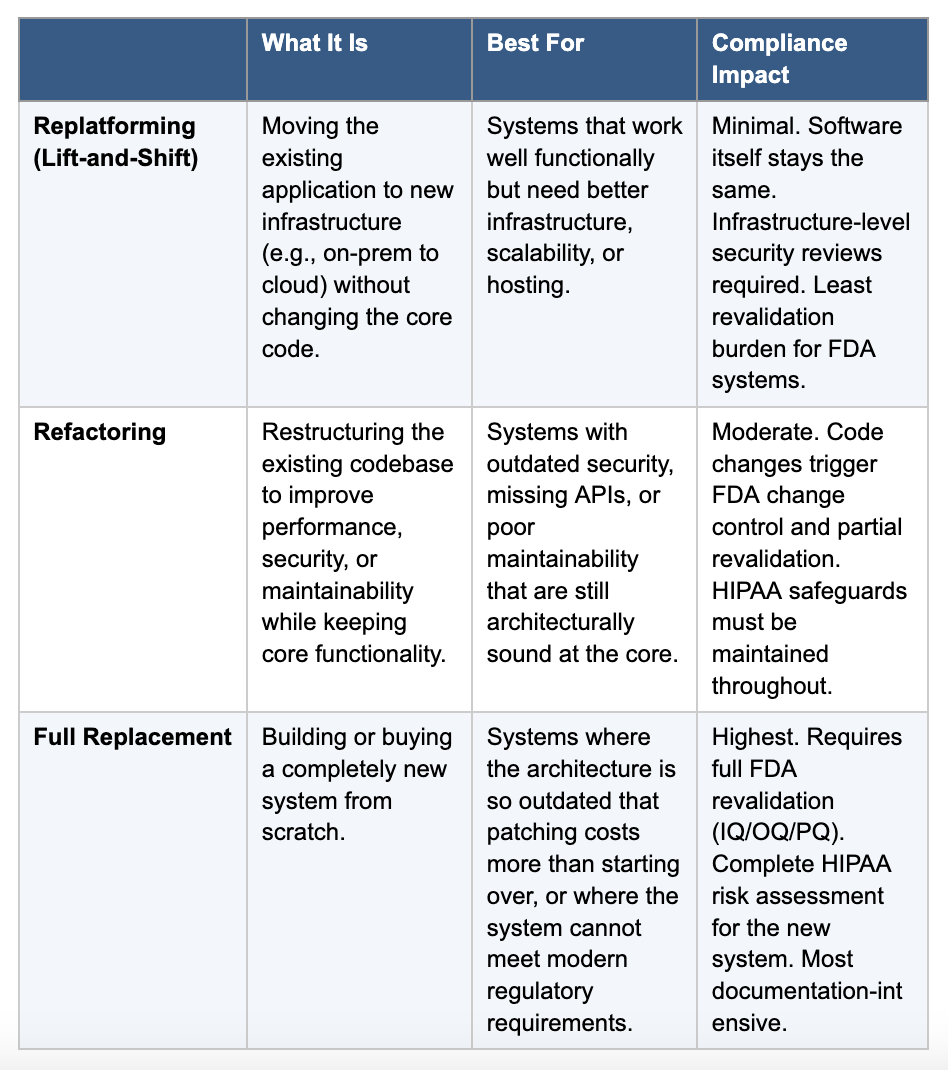 Note: For FDA-regulated software, refactoring and replacement both trigger significant revalidation requirements. Factor that into your timeline and budget from the start.
Note: For FDA-regulated software, refactoring and replacement both trigger significant revalidation requirements. Factor that into your timeline and budget from the start.
Phased Implementation vs. Big Bang
A phased approach breaks the modernization into manageable stages. You migrate one module or subsystem at a time, validate it, confirm compliance, and then move to the next. This keeps healthcare operations running and gives your team a chance to catch problems early. The “big bang” approach, switching everything at once, can work for smaller systems, but it is high-risk in healthcare. If something goes wrong on launch day and clinicians cannot access patient records, you have a patient safety issue on your hands that could lead to medical errors and compromised patient outcomes. Most experienced healthcare software development teams will recommend a phased strategy for exactly this reason.Technical Implementation That Keeps You Compliant
This is where compliance is won or lost. The technical choices you make during implementation will determine whether your modernization project stays compliant or creates new vulnerabilities. Below is a step-by-step breakdown of the three main technical workstreams.Step 1: Data Migration Without Breaking HIPAA
Data migration in healthcare is a compliance event as much as it is an IT task. Every record you move contains PHI, and every step of the extraction, transformation, and loading (ETL) process needs to be secured and documented. What to do:- Encrypt everything. All PHI must be encrypted in transit (TLS 1.2+) and at rest (AES-256). No exceptions.
- Log all access. Maintain detailed access logs throughout the migration, like who accessed what data, when, and why.
- Validate at each stage. Run automated data validation checks after extraction, after transformation, and after loading to confirm nothing was corrupted, duplicated, or lost.
- Prepare rollback procedures. Test your ability to revert to the original system before you begin. If migration fails midway, you need a clean fallback.
- Run parallel environments. Operate both old and new systems simultaneously for a period so you can compare outputs and catch discrepancies before transitioning over.
- Map data fields explicitly. Document how every data field in the old system maps to the new one. Flag any fields that change format, merge, or split. These are common sources of data integrity issues.
Step 2: Cloud Migration
Moving healthcare workloads to the cloud is one of the most common modernization strategies, and for good reason. It improves scalability, reduces operational costs, and can actually strengthen your security posture if done right. What to do:- Require a signed BAA from your cloud provider. AWS, Azure, and GCP all offer HIPAA-eligible services, but you must have a BAA in place before any PHI touches the cloud.
- Understand data residency requirements. Where your data physically lives matters for compliance. Some regulations and organizational policies require data to stay within specific geographic regions.
- Pursue HITRUST certification. HITRUST CSF has become the de facto security framework for healthcare cloud environments. It maps to HIPAA, NIST, and other frameworks, which simplifies audits.
- Configure cloud-native security tools. Use the provider’s built-in encryption, key management, identity and access management (IAM), and audit logging. Do not rely solely on your application-layer security.
Step 3: Integration for Hybrid Environments
In most modernization projects, you will be running old and new systems side by side for a while. This hybrid environment needs a solid integration strategy to keep data flowing and compliance intact. What to do:- Use API-based integration as your default. APIs let modern and legacy components communicate through well-defined interfaces. They are the cleanest option for maintaining data consistency across systems.
- Deploy middleware where APIs are not available. When legacy systems do not support modern APIs, middleware (such as an integration engine like MuleSoft or Rhapsody) can bridge the gap.
- Ensure real-time or near-real-time data synchronization. Stale data in a hybrid environment creates clinical risk. Set up event-driven or polling-based sync depending on your system capabilities.
- Extend audit logging across both environments. Your compliance audit trail must cover the full data path, from the legacy system through the integration layer to the new system. Gaps in logging are gaps in compliance.
Testing and Validation Protocols
Testing in a healthcare software modernization project is not the same as testing a consumer app. The stakes are higher, the documentation requirements are more demanding, and the regulators expect to see proof that you did it right. For FDA-regulated systems, the traditional approach follows the IQ/OQ/PQ model:- Installation Qualification (IQ): Confirms the system is installed correctly in the target environment.
- Operational Qualification (OQ): Verifies it works as intended under expected operating conditions.
- Performance Qualification (PQ): Proves it performs reliably under real-world conditions with actual clinical workflows.
Kanda in Action: Engineering Takeover for a Global Healthcare Platform
Modernizing legacy healthcare software sounds great on paper, but what does it look like when someone actually does it? One example from Kanda involved a globally recognized healthcare solutions provider whose mobile applications and backend services were struggling under a legacy codebase maintained by a previous vendor. The challenge was significant. The company needed a full engineering takeover, transitioning development responsibility for two mobile applications and supporting backend services, without disrupting ongoing operations. The existing codebase was complex and poorly documented, the system had lots of technical debt, and the transition had to be handled with complete discretion. What Kanda did:- Assembled three specialized engineering teams (22 people total) within 60 days.
- Set up a parallel software and hardware environment mirroring the existing setup, allowing deep architectural analysis before making changes.
- Implemented Agile/Scrum with Jira tracking, creating transparent workflows that aligned expectations around what the legacy system could realistically deliver.
- Maintained strict adherence to healthcare compliance, like HIPAA, FDA regulations for digital therapeutics, and standard data privacy protocols, throughout the entire transition.
- Used AWS services for scalability and security, supporting parallel development and accelerating time-to-market.
- Seamless engineering transition with zero operational disruption
- Improved predictability in feature releases
- Higher product quality with fewer customer complaints
- Strengthened client relationships
How Kanda Can Help
Legacy healthcare software modernization is a complex project that touches engineering, compliance, data security, and clinical operations all at once. Kanda has been working in healthcare software development for decades, and we bring the kind of cross-functional expertise that healthcare leaders need for these projects. We can support in:- Assessing your legacy systems and identifying the highest-priority modernization targets based on technical risk and compliance exposure.
- Designing and executing phased modernization strategies that maintain FDA and HIPAA compliance at every stage.
- Engineering complex system transitions, including full engineering takeovers, without disrupting clinical operations.
- Implementing secure data migration, cloud migration, and electronic health records (EHR) integration with proper validation and documentation.
- Building modern, scalable architectures that are compliant by design and ready for future regulatory changes.
Conclusion
Legacy healthcare software is not going to fix itself. The technical risks compound, the compliance gaps widen, and the costs keep climbing the longer you wait. But modernization does not have to be a reckless leap. With the right approach, like a clear assessment, a phased plan, and compliance built into every step, it is entirely possible to transform outdated systems into modernized systems that are more secure, more efficient, and fully compliant with FDA and HIPAA requirements. The organizations that achieve a successful transformation share a few things in common: they start with honest assessments of where they stand, they invest in the right expertise, and they treat compliance not as an obstacle but as a design constraint that leads to better patient outcomes.Related Articles

CMS Prior Authorization Rule 2026: What Health Systems and Payers Actually Need to Build by October 2027
Key Takeaways The 2026 CMS Prior Authorization (CMS-0062-P) rule extends electronic prior authorization requirements to drugs for the first time, closing a major gap left by the 2024 rule. The hard compliance deadline is October 1, 2027 - by that date, systems must be live, not in development or testing. Compliance requires three major technical…Learn More
Unlocking Actionable Insights from Medical Data with Clinical NLP
Key Takeaways Clinical NLP extracts useful details from notes, reports, and other free-text records so teams can work with them. The clearest use cases include coding support, trial matching, safety monitoring, registry work, and population health. The output is only useful if it connects to the standards healthcare teams already use: SNOMED CT, RxNorm, LOINC,…Learn More
Why Omics and Clinical Data Integration Remain a Challenge and How to Fix It
Key Takeaways Omics and clinical data often remain separate, making them harder to use together than they should be. The main challenge is usually not the data itself, but the mismatched formats, siloed systems, and disconnected teams surrounding it Addressing that requires robust infrastructure, shared standards, and workflows that hold up without constant manual intervention.…Learn More
AI Copilots in Healthcare: Minimizing Diagnostic Risks With Smart Virtual Assistants
Key Takeaways AI copilots act as always-on virtual assistants managing documentation, triage, and decision support so clinicians can focus on patients. With 12 million diagnostic errors and up to 80,000 deaths annually, AI copilots are built to catch what overloaded clinicians miss, not replace them. Dragon Copilot saves clinicians around 5 minutes per encounter with…Learn More

